Why You Want the Hackers in White Hats to Break into Your System
In old western movies, it was easy to tell the good guys from the bad. You just had to check out their hats. Black hat meant bad guy. White hat meant good guy.
In a much more metaphorical way, the same is true for hackers. A black hat hacker is a criminal who breaks into networks to steal data for their own use or to sell to other criminals. A white hat hacker (also known as an ethical hacker) is doing the same thing, but with a very different intent.
The only way to understand the security of a device is to test it. And to determine the protection that might be needed, you have to think like a black hat hacker. An ethical hacker has to take note of what the black hat hackers are doing and what tools they are using, so that the true owner of the information can take action to protect themselves.
A growing need for protection
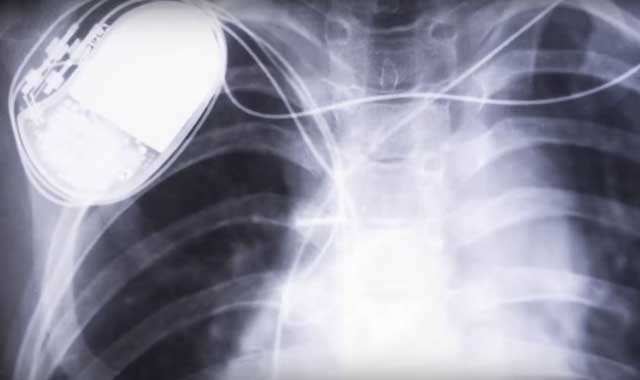
The medical industry is one area where hacking is on the rise. Nearly every medical device has some sort of connectable technology in it, and everyone’s medical records are now digital. In most reported successful attacks, the hackers were after patient data. That data is very valuable on the black market.
For example, if a hacker steals someone’s credit card number, the card can quickly be canceled. But if a hacker steals someone’s personal background information (social security number, current and former addresses, medical history, etc.), an unlimited number of credit cards can be opened in that person’s name.
Solving the security puzzle
Hacking is really just solving a puzzle. “It’s how can I outthink the person who designed this system. It’s reverse engineering to figure out how I can manipulate your system without your help – basically how I can make it do what I want,” said Stephanie Domas, a certified ethical hacker at Battelle. Stephanie spends most of her time in her white hat focused on medical device security.
She’s looking at:
Who – Is it a teenager in his parents’ basement or a high-powered black hat hacker from a foreign nation?
What – What information is at risk? Is it something specific to the device, such as changing the way the device works, or is it an attempt to gain access to a hospital network?
Where – Where are the weak spots in the device? Is the cyber security problem a flaw in the design? What other ways would a hacker be able to access data?
No medical device can be 100 percent secure. There is a trade off when it comes to usability vs. security and manufacturers have to accurately assess the risks for their devices. But Stephanie’s job, and all the other white hat hackers out there, are needed to help determine the risks and how they can be minimized to ensure patient safety and information security.
Related Blogs
BATTELLE UPDATES
Receive updates from Battelle for an all-access pass to the incredible work of Battelle researchers.